Windows Control Series
Posted: June 23, 2012
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Ranking: | 8,721 |
|---|---|
| Threat Level: | 2/10 |
| Infected PCs: | 4,401 |
| First Seen: | June 23, 2012 |
|---|---|
| Last Seen: | September 22, 2023 |
| OS(es) Affected: | Windows |
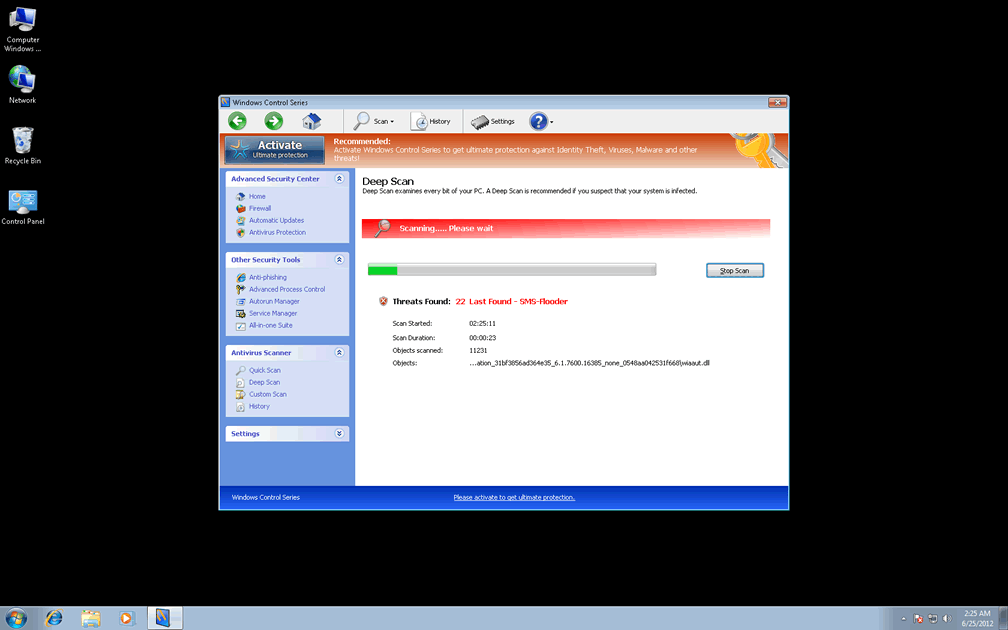
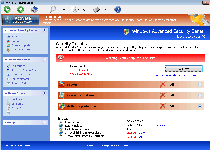 While Windows Control Series looks like an anti-malware product that could theoretically detect and remove all sorts of PC threats from phishing-based attacks to rootkits, SpywareRemove.com malware analysts have confirmed Windows Control Series's membership in FakeVimes, making Windows Control Series no better than scamware. Like similar rogue anti-malware scanners, Windows Control Series isn't able to offer legitimate security information and prefers to display alerts about PC threats, attacks and infections that actually aren't on your computer in the first place. Given this, spending money on a registration key for Windows Control Series is strongly discouraged, despite Windows Control Series's frequent requests for you to do exactly that as a way to save your PC from problems that don't exist. As a member of a scamware family that's known for causing security issues, including browser redirect attacks, Windows Control Series should be deleted as soon as you can gain access to a reputable anti-malware scanner that can perform the operation.
While Windows Control Series looks like an anti-malware product that could theoretically detect and remove all sorts of PC threats from phishing-based attacks to rootkits, SpywareRemove.com malware analysts have confirmed Windows Control Series's membership in FakeVimes, making Windows Control Series no better than scamware. Like similar rogue anti-malware scanners, Windows Control Series isn't able to offer legitimate security information and prefers to display alerts about PC threats, attacks and infections that actually aren't on your computer in the first place. Given this, spending money on a registration key for Windows Control Series is strongly discouraged, despite Windows Control Series's frequent requests for you to do exactly that as a way to save your PC from problems that don't exist. As a member of a scamware family that's known for causing security issues, including browser redirect attacks, Windows Control Series should be deleted as soon as you can gain access to a reputable anti-malware scanner that can perform the operation.
Windows Control Series: a Fraud in a Microsoft-Lookalike Suit
As is true for many other members of FakeVimes, Windows Control Series borrows the superficial looks of Windows Security Center to make itself look more trustworthy than Windows Control Series actually is. With only minor additions such as anti-phishing and memory-monitoring features, Windows Control Series comes off as an expansive security and anti-malware suite, but its threat-detection capabilities are entirely fraudulent. While Windows Control Series is active, Windows Control Series will display pop-up alerts, taskbar-based balloons and other security warnings about attacks against Windows components, identity theft and the presence of various types of harmful software, but these pop-ups should be disregarded as erroneous. Likewise, Windows Control Series's system scans may superficially look like real results, but have no ability to help your PC, since they're designed to display Trojans and other infections without any attempt at accuracy. SpywareRemove.com malware experts have found that since Windows Control Series launches itself automatically, these symptoms will tend to display themselves regularly unless you make an explicit effort at blocking Windows Control Series.
Windows Control Series's main intent is to steal money in its fake registration process, and although SpywareRemove.com malware experts warn against giving any financial information to Windows Control Series's company, faking Windows Control Series's registration can be helpful to ease its removal. Entering the code '0W000-000B0-00T00-E0020' can accomplish this for both Windows Control Series and other FakeVimes-based scamware, including Privacy Guard Pro, PrivacyGuard Pro 2.0, Extra Antivirus, Fast Antivirus 2009, Presto TuneUp, Windows Security Suite, Smart Virus Eliminator, Packed.Generic.245, Volcano Security Suite, Windows Enterprise Suite, Enterprise Suite, Additional Guard, Live PC Care, PC Live Guard, Live Enterprise Suite, Security Antivirus, My Security Wall, CleanUp Antivirus and Smart Security.
What to Do When Windows Control Series Takes Control of Your PC Away from You
The obvious symptoms of a Windows Control Series infection may include fake security functions, but Windows Control Series can also play party to more dangerous attacks than those previously listed. Some of the top security issues that SpywareRemove.com malware researchers have associated with Windows Control Series and its clones include, but aren't limited to:
- Browser redirects to sites that promote Windows Control Series, spam search engines that profit off of your unwilling traffic and fake error pages (the latter often being included to block you from visiting legitimate security sites).
- Deleted Registry entries for legitimate programs, including firewall tools, anti-virus scanners and similar security-related applications. This will cause these programs to fail to function unless the relevant entries are restored or your programs are re-installed.
- Programs may also be blocked by Windows Control Series from memory. Unlike the above attack, this form of block doesn't damage Windows components or your application, although you may be unable to launch the program until you've shut Windows Control Series down.
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%APPDATA%\Protector-khea.exe
File name: Protector-khea.exeSize: 2.11 MB (2119680 bytes)
MD5: 80cf516fd3763964c13fd85bf252c2df
Detection count: 84
File type: Executable File
Mime Type: unknown/exe
Path: %APPDATA%
Group: Malware file
Last Updated: June 25, 2012
%AppData%\Protector-[RANDOM CHARACTERS].exe
File name: %AppData%\Protector-[RANDOM CHARACTERS].exeFile type: Executable File
Mime Type: unknown/exe
Group: Malware file
Registry Modifications
HKEY..\..\{Value}HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\Inspector = %AppData%\Protector-[RANDOM CHARACTERS].exeHKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\alertsvc.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Ad-Aware.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\agent.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\aAvgApi.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\alogserv.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\About.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AdwarePrj.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AlphaAV\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\adaware.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\agentw.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ackwin32.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\alevir.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AAWTray.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\advxdwin.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\AlphaAV.exe\"Debugger" = "svchost.exe"HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\a.exe\Debugger = svchost.exeHKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\agentsvr.exe\"Debugger" = "svchost.exe"
Additional Information
| # | Message |
|---|---|
| 1 | Error Attempt to modify registry key entries detected. Registry entry analysis is recommended. |
| 2 | Error Keylogger activity detected. System information security is at risk. It is recommended to activate protection and run a full system scan. |
| 3 | Warning Firewall has blocked a program from accessing the Internet C:program filesinternet exploreriexplore.exe is suspected to have infected your PC. This type of virus intercepts entered data and transmits them to a remote server. |
Leave a Reply
Please note that we are not able to assist with billing and support issues regarding SpyHunter or other products. If you're having issues with SpyHunter, please get in touch with SpyHunter customer support through your SpyHunter . If you have SpyHunter billing questions, we recommend you check the Billing FAQ. For general suggestions or feedback, contact us.