Ukash Virus
Posted: July 15, 2012
Threat Metric
The following fields listed on the Threat Meter containing a specific value, are explained in detail below:
Threat Level: The threat level scale goes from 1 to 10 where 10 is the highest level of severity and 1 is the lowest level of severity. Each specific level is relative to the threat's consistent assessed behaviors collected from SpyHunter's risk assessment model.
Detection Count: The collective number of confirmed and suspected cases of a particular malware threat. The detection count is calculated from infected PCs retrieved from diagnostic and scan log reports generated by SpyHunter.
Volume Count: Similar to the detection count, the Volume Count is specifically based on the number of confirmed and suspected threats infecting systems on a daily basis. High volume counts usually represent a popular threat but may or may not have infected a large number of systems. High detection count threats could lay dormant and have a low volume count. Criteria for Volume Count is relative to a daily detection count.
Trend Path: The Trend Path, utilizing an up arrow, down arrow or equal symbol, represents the level of recent movement of a particular threat. Up arrows represent an increase, down arrows represent a decline and the equal symbol represent no change to a threat's recent movement.
% Impact (Last 7 Days): This demonstrates a 7-day period change in the frequency of a malware threat infecting PCs. The percentage impact correlates directly to the current Trend Path to determine a rise or decline in the percentage.
| Ranking: | 595 |
|---|---|
| Threat Level: | 9/10 |
| Infected PCs: | 130,111 |
| First Seen: | August 8, 2012 |
|---|---|
| Last Seen: | January 8, 2024 |
| OS(es) Affected: | Windows |
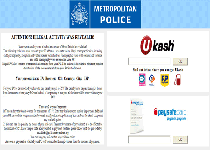 The Ukash Virus is a colloquial nickname for a family of ransomware Trojans that display fraudulent police alerts, block you from using other applications and threaten you with legal action if you don't pay a fee within a short time period. Preferred payment methods for this fine include Paysafecard and Ukash – hence the Ukash Virus's name. The Ukash Virus family is especially notable for tailoring its warning messages to local regions and having many different variants for different countries. SpywareRemove.com malware researchers have noted that the Ukash Virus is particularly widespread in Europe, but there are also variants of the Ukash Virus that are designed for American or Canadian PCs. If you see a warning message that resembles a Ukash Virus's pop-up, you should, firstly, try to disable the Ukash Virus, and secondly, use appropriate anti-malware software to delete the Ukash Virus infection. Under no cases should you ever feel it necessary to pay a Ukash Virus fine, which is, itself, an illegal request.
The Ukash Virus is a colloquial nickname for a family of ransomware Trojans that display fraudulent police alerts, block you from using other applications and threaten you with legal action if you don't pay a fee within a short time period. Preferred payment methods for this fine include Paysafecard and Ukash – hence the Ukash Virus's name. The Ukash Virus family is especially notable for tailoring its warning messages to local regions and having many different variants for different countries. SpywareRemove.com malware researchers have noted that the Ukash Virus is particularly widespread in Europe, but there are also variants of the Ukash Virus that are designed for American or Canadian PCs. If you see a warning message that resembles a Ukash Virus's pop-up, you should, firstly, try to disable the Ukash Virus, and secondly, use appropriate anti-malware software to delete the Ukash Virus infection. Under no cases should you ever feel it necessary to pay a Ukash Virus fine, which is, itself, an illegal request.
The Ukash Virus: a Globetrotter with Crime on Its Mind
Variants of the Ukash Virus may be distributed in a number of ways, although SpywareRemove.com malware researchers have noted that many recent Ukash Virus attacks have involved drive-by-download exploits from malicious websites. Ukash Virus infections are immediately noticeable due to their primary symptom: an HTML page that covers your entire desktop and Windows interface. This web page is crafted to look like a country-specific legal warning against embarrassing or common crimes such as child pornography trafficking or illegal music downloads. Most variants of Ukash Virus pop-ups will also display your IP address, some will display a fake 'video recording' notice, and all of them will claim to be from some form of unrelated law enforcement organization.
Examples of the widespread and nationality-tailoring nature of individual Ukash Viruses include:
- The Scotland Yards Ukash Virus, West Yorkshire Ransomware, Metropolitan Police Ukash Virus, Police Central e-crime Unit (PCEU) ransomware ransomware, which target the United Kingdom.
- Athens Security Prosecution of Electronic Crime Ransomware, which targets Greece.
- Bundespolizei National Cyber Crimes Unit Ransomware, one of the earliest detected variants of the Ukash Virus, which targets Germany. This is along with other German variants of the Ukash Virus, such as GVU Gesellschaft zur Verfolgung Ransomware.
- 'Attention! Votre ordinateur a ete pour violation' ransomware, Votre ordinateur est bloqué Gendarmerie Ransomware, Police Nationale FR Ransomware, Office Central de Lutte contre la Criminalité Ransomware, Gendarmerie Nationale Ransomware and Sacem Police Nationale Ransomware, all of which target France.
- 'Votre ordinateur est bloqué' Belgium Ransomware, which targets Belgium.
- Polícia de Segurança Pública Portuguese Virus, which targets Portugal.
- Royal Canadian Mount Police (RCMP) Ransomware and the Canadian Security Intelligence Service (CSIS) Ransomware, which target Canada.
- Poliisi Tietoverkkorikos Tutkinnan Yksikkö Ransomware, which targets Finland.
- The Cuerpo Nacional de Policia Virus
- Guardia di Finanza Ransomware, Polizia postale e delle communicazioni Ransomware and 'Il Suo computer e'stato bloccato' Ransomware, which target Italy.
- 'Computer Crime & Intellectual Property Section' Ransomware, which targets the United States.
- Computerkriminalitat Des Criminal Intelligence Service Ransomware, which targets Austria.
- Politie Federal Computer Crime Unit Ransomware, which targets the Netherlands.
- Polisen Enhetnen för Databrott Ransomware, which targets Sweden.
Where the Buck Stops with the Ukash Virus
Although Ukash Virus pop-ups claim to have legal authority and may even warn you of consequences to your PC (such as file deletion) if you don't pay their fines, you should never feel the need to pay the ransom from Ukash Virus infections or other ransomware attacks. Resolutions to most Ukash Virus problems are easier to find than you might expect, since SpywareRemove.com malware researchers have found that common variants of the Ukash Virus only use their pop-ups to block other programs and, therefore, can be disabled to renew complete access to your PC. No known variants of the Ukash Virus actually possess any ability to carry out their threats, and ignoring their warnings is safer for both your PC and bank account than the converse.
Disabling the Ukash Virus is achievable through various methods, with popular techniques including booting to Safe Mode or booting Windows from a USB-based HD device. Since recent Ukash Virus infections have been distributed via browser exploits, SpywareRemove.com malware research team stresses that having good browser settings and a strong anti-malware program to block drive-by-downloads can help to prevent your PC from being the Ukash Virus's next target. In spite of their nicknames, Ukash Virus-based PC threats aren't true viruses and do not have any known ability to infect wide varieties of other files.
Aliases
More aliases (821)
Technical Details
File System Modifications
Tutorials: If you wish to learn how to remove malware components manually, you can read the tutorials on how to find malware, kill unwanted processes, remove malicious DLLs and delete other harmful files. Always be sure to back up your PC before making any changes.
The following files were created in the system:%SystemDrive%\Users\<username>\AppData\Local\Temp\vE0f7hC.exe
File name: vE0f7hC.exeSize: 122.36 KB (122368 bytes)
MD5: 9ae84c87978d6009950e02256cacfd4e
Detection count: 85
File type: Executable File
Mime Type: unknown/exe
Path: %SystemDrive%\Users\<username>\AppData\Local\Temp
Group: Malware file
Last Updated: July 19, 2013
MSPAINT.EXE
File name: MSPAINT.EXESize: 209.4 KB (209408 bytes)
MD5: d3448fb158b500704144fd75ec94c189
Detection count: 82
File type: Executable File
Mime Type: unknown/EXE
Group: Malware file
Last Updated: January 9, 2014
%APPDATA%\Microsoft\Windows\Templates\securitywindrv.exe
File name: securitywindrv.exeSize: 34.81 KB (34816 bytes)
MD5: 0da8705f12382804c87d20ee58a4674c
Detection count: 56
File type: Executable File
Mime Type: unknown/exe
Path: %APPDATA%\Microsoft\Windows\Templates
Group: Malware file
Last Updated: August 22, 2013
%ALLUSERSPROFILE%\lwo8z8rcl.dss
File name: lwo8z8rcl.dssSize: 204.8 KB (204800 bytes)
MD5: 496fea09b09d07f7b3a9d3834229702f
Detection count: 53
Mime Type: unknown/dss
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: November 25, 2013
bunk.exe
File name: bunk.exeSize: 61.44 KB (61440 bytes)
MD5: bb29ba1cad79dcb26c986ecc92d76b4e
Detection count: 45
File type: Executable File
Mime Type: unknown/exe
Group: Malware file
Last Updated: August 8, 2013
Other.res
File name: Other.resSize: 230.4 KB (230400 bytes)
MD5: bf230af91ac92924a745f42021abbba0
Detection count: 41
Mime Type: unknown/res
Group: Malware file
Last Updated: December 16, 2014
%APPDATA%\Other.res
File name: Other.resSize: 70.65 KB (70656 bytes)
MD5: 2122654109b372638bca24f780ea1921
Detection count: 21
Mime Type: unknown/res
Path: %APPDATA%
Group: Malware file
Last Updated: November 11, 2013
C:\ProgramData\F5753306.cpp
File name: F5753306.cppSize: 241.84 KB (241848 bytes)
MD5: 12f3c8bc428f4e2c2b547cc20ac6db87
Detection count: 20
Mime Type: unknown/cpp
Path: C:\ProgramData
Group: Malware file
Last Updated: October 31, 2014
%ALLUSERSPROFILE%\bf8h8d02hf.exe
File name: bf8h8d02hf.exeSize: 315.9 KB (315904 bytes)
MD5: 1cbe49c0ebbeefbbe9f1c1fda9eebbe6
Detection count: 19
File type: Executable File
Mime Type: unknown/exe
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: November 13, 2014
%ALLUSERSPROFILE%\hwj3ba6j.dss
File name: hwj3ba6j.dssSize: 176.64 KB (176640 bytes)
MD5: 54f1a99f7cb18ed47756bb22e1681766
Detection count: 7
Mime Type: unknown/dss
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: November 4, 2013
%ALLUSERSPROFILE%\dxrqfya.exe
File name: dxrqfya.exeSize: 57.34 KB (57344 bytes)
MD5: 85f908a5bd0ada2d72d138e038aecc7d
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: September 9, 2020
%SystemDrive%\Users\<username>\AppData\Local\Temp\xaZYOVJW.exe
File name: xaZYOVJW.exeSize: 133.63 KB (133632 bytes)
MD5: 4382872727fc8c0996fa315c599ecdf0
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %SystemDrive%\Users\<username>\AppData\Local\Temp
Group: Malware file
Last Updated: September 16, 2013
%ALLUSERSPROFILE%\dqnbdq7.dss
File name: dqnbdq7.dssSize: 175.61 KB (175616 bytes)
MD5: 6514a485b26fcca011121f42f188d3b2
Detection count: 5
Mime Type: unknown/dss
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: November 18, 2013
%ALLUSERSPROFILE%\ActiveU0\bzsbkotiu.exe
File name: bzsbkotiu.exeSize: 233.47 KB (233472 bytes)
MD5: 35180a38939fe1b4368d804ae25e5a57
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %ALLUSERSPROFILE%\ActiveU0
Group: Malware file
Last Updated: December 2, 2013
%ALLUSERSPROFILE%\Data aplikac?\wjthvwjb.dss
File name: wjthvwjb.dssSize: 221.18 KB (221184 bytes)
MD5: 9f2da2fd4fe9713d74acf0eb8fad8dc3
Detection count: 5
Mime Type: unknown/dss
Path: %ALLUSERSPROFILE%\Data aplikac?
Group: Malware file
Last Updated: November 22, 2013
%ALLUSERSPROFILE%\r90lwlww.dss
File name: r90lwlww.dssSize: 208.89 KB (208896 bytes)
MD5: dbc66a280086ab3c23c2dca7b49fa96c
Detection count: 5
Mime Type: unknown/dss
Path: %ALLUSERSPROFILE%
Group: Malware file
Last Updated: November 25, 2013
%USERPROFILE%\Local Settings\Temp\msavfit.exe
File name: msavfit.exeSize: 158.2 KB (158208 bytes)
MD5: 9f5e6c75851b2ee4b10e3e3b783d10b7
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %USERPROFILE%\Local Settings\Temp
Group: Malware file
Last Updated: November 13, 2014
%WINDIR%\system32\audipbrd.exe
File name: audipbrd.exeSize: 347.64 KB (347648 bytes)
MD5: 6ea827e7f4d182b0cb538cb5048bbdb2
Detection count: 5
File type: Executable File
Mime Type: unknown/exe
Path: %WINDIR%\system32
Group: Malware file
Last Updated: December 22, 2014
More files
Registry Modifications
Regexp file mask%ALLUSERSPROFILE%\[RANDOM CHARACTERS].bat%ALLUSERSPROFILE%\dsgsdgdsgdsgw.bat%AllUsersProfile%\Local Settings\Temp\[RANDOM CHARACTERS].pif%ALLUSERSPROFILE%\lsass.exe%ALLUSERSPROFILE%\ms[RANDOM CHARACTERS].dat%APPDATA%\[RANDOM CHARACTERS].dll%APPDATA%\csrsss.exe%AppData%\Other.res%APPDATA%\skype.dat%APPDATA%\system\winlogon.exe%APPDATA%\updates\[RANDOM CHARACTERS].exe%APPDATA%\wgsdgsdgdsgsd.exe%LOCALAPPDATA%\Temp\ms[RANDOM CHARACTERS].com%TEMP%\msimg32.dll%TEMP%\wpbt0.dll
Related Posts
- Mukashi
- West Mercia Police Ukash Virus
- United Kingdom Police Ukash Virus
- Polska Policja Ukash Virus Ransomware
- Ukash Paysafecard Virus Ransomware
I was a victim of ukash today, I paid 100 pounds to remove it from my computer although
i have mcaffee anti virus on my computer is there anything i can do about this?, thanks fred
I have been a victim of the virus and swidled out of 100 pounds. can you tell me what i can do about this, my payment was through paypoint vouchers, transaction 69779 on 7/8/12 please advise
same. i paid 100 euro to unlock vomputer. Any risk for further damage ? bank acount intrusion ?
i have been a victin twice to the police ukash virus and the best solution is to download anti-malware its free and can catch any virus that is trying to stop you using your laptop,can only be used in safe mode if u have virus.
Today my laptop was blocked by this virus. Fortunately I did not paid only because my wife was suspicious why the police does not give an option the fine to be paid on line. It makes sense.
I had UCASH on my XP desktop - what a pain - I looked at some recommendations but did my own thing. I simply went to an old RESTORE POINT which got rid. Having done that I realised there was a risk so also, as I had access to all my current files, decided to back-up and format my drive to be absolutely sure. I mentioned this as anyone caught will not have access to anything but booting up and F8 restore might buy you time to save stuff and then go for fdisk, the only real way to erase everything.
how do you remove this virus and how can I get my money back
Caro vladimir, o que você fez para o virus sair do seu pc?
Eu com o virus nao consigo executar qualquer programa
F8 does not always solve this as it does not always allow enough time to back up. My suggestion is have the operating system on a partition on your hard drive and have a seperate hard drive for programs and data. If you do get infected, use the HARD DRIVE MANUFACTURERS software, eg Seagate drive Seatools, Western Digital drive DataLifeguard, to erase the drive, writing x's or 1's to every sector. I know this is a pain, cos you then have to re-install your operating system and your programs. Windows OS takes about an hour, but that is a lot better than 100 quid. I have just done this !
Just recieved the virus here in Valencia Spain, second time of having it! First time it took over hole screen but after a frantic couple of hours of translating the page I discovered it was a virus so after swithing lap top off and on the antivirus took over and got rid of it for me. This time it's taken over the hole screen again but this time it has turned my cam on trying to film me!!! and anti virus isn't working!!!! ...doh! Nice seeing this site though being reminded that it is an annoying and scary 'prank'!!!
I am a victim of ucash virus,I paid 100 euros to remove virus but it will not take voucher no.
7180257974767228
I got the UKASH malware on my computer a couple of days ago. I quickly realised it was a half-arsed attempt to extort money with no legal validity.It only seems to have invaded MY log on, not my wife's (ok prolly via a bit of porn - sue me!). I have found a short term solution, which is to log on, open some stuff on my desktop before the UKASH page catches me and then, when it catches up, press the off button on my comp very quickly. What happens is my desktop comes back with the things I've opened (explorer, i-tunes, skype etc) just for a couple of seconds. If I can start working on them very quickly - start playing a tune in I tunes, type a browse subject in google, or call someone in skype - the comp doesnt close down and UKASH goes away for one session. Obv. I need a longer term solution, so I'll be downloading the above
ukash is the biggest scam to hit uk through western union bank, if you hsve psid for your voucher using a credit or debit card you are at risk of identity theft. i know this through experience of customer feed back of where i work. ukash vouchers used to be a viable way to pay for things online untill these scams came on the go. newest one to date, if you have been online looking for finance, they phone, verify bank details so you can receive funds, then purchase a voucher to make your first months payment to them, your so wrapped up with what they are offering, you dont realise YOU, gave them your bank details, like my husband 3 mnths ago!!!! took 24 hrs to wipe out our bank account and 6wks to reclaim 1/3rd of our money back
i just got this today after i relised it was a scam i turned off my pc rebooted and done a system restore and all seems fine i dunn know if i have gotten it compleatly out but luckly i have full back up off all my programs and games ect on disk just wondering if any1 has tried a factory default reset just wondering if that would wipe it out 100%
****** schedcli is a New Ukash Filename ********
***************************************************
The UKASH virus is pretty smart because the hackers
have compiled the code to adapt to different operating systems &
software platforms & also detect PC users geographical location
in order to make the annoying banner Country(Region) specific.
As was stated earlier the UKASH application
has lots of different file names and will embeded itself in different
directory locations depending on the PC's O/S, using it's different filenames.
ANOTHER UKASH FILE NAME IS FOUND ON VISTA & WINDOWS 7 IS:
schedcli
However there is currently a pattern that is common to all UKASH Ransomeware
virus files. To find out the file name and location of the virus
on a Windows plaform, follow these simple steps:
run the infected laptop in SAFEMODE.
(1) re-boot laptop > immediately during bootup press & hold the F8
button until you hear a beep, then unpress the F8 button
(2) Once in SAFEMODE, nagivate to run command, there are two
ways to get to run, hold down the windows symbol key + r together or
go to start & type run
(3) in the run command type msconfig.exe and hit return
(4) You are now in the system configuration window, nagivate
to the startup tab. Look for any application that you do not
recognize and the manufacturer is stated as UNKNOWN.
Be very careful when investigating & performing this process
especially if you have installed lots of jail broken, cracked or
unlicensed applicaitons.
(5) The UKASH file will normally be installed in Appdata directory
under the account name being used when the laptop became infected.
For Windows Vista and WIndows 7 the UKASH Virus locations are:
WINDOWS DIRECTORY
c:\users\<username>\Appdata\Local\Microsoft\Windows\1592\schedcli.exe
(REMEMBER the .exe filename could be different)
REGISTRY:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Shared Tools\MSConfig\startupreg\schedcli
MODIFYING\REMOVING REGISTRY DIRECTORIES & HIVE KEYS SHOULD ONLY BE PERFORMED IF YOU ARE A VERY EXPERIENCED,
HIGHLY COMPETENT I.T. USER AND KNOW WHAT YOU ARE DOING, SINCE MODIFING\REMOVING ANY REGISTRY DIRECTORY OR HIVE KEY
BY MISTAKE WILL SERIOUS DAMAGE YOUR PC, WHICH COULD RENDER IT TOTALLY INOPERABLE (NOLONGER WORKING OR FUNCTIONING),
DUE TO THE ACCIDENTAL DELETION\MODIFICATION OF VERY IMPORTANT SYSTEM\PROGRAM FILES, NOT TO MENTION A SIGNIFICANT LOSS OF
PERSONAL DATA WHICH COULD RESULT IN THE OPERATING SYSTEM BECOMING UNSTABLE AND NEEDING A COMPLETE RE-INSTALLATION OF THE OPERATING SYSTEM
THEREFORE, IT IS RECOMMENDED THAT LESS EXPERIENCED I.T. PERSONS SHOULD USE ANY NUMBER OF VERY GOOD MALWARE\VIRUS REMOVAL TOOLS IN ORDER TO
REMOVE THE UKASH VIRUS.
GOOD LUCK : )
ive deleted like half my stuff and removed the virus/trojan now my internet doesnt work any1 kno y is tht? maybe i deleted something wrong?
Perhaps I am naive but I think it should be possible for UKash to identify the scammers and at least stop transacting payments to them. They should also assist the authorities to bring them to Justice. This of course assumes that UKash is a legitimate finance organization and is not in league with the criminals.
I cannot believe you people who actually paid !
All you needed to do was restart your Pc in Safe-Mode and then run your virus scanner or remove the virus manually as i have just done. As suggested it's easy to find the startup file and then you have th random .exe name. Search it out and delete it. Then search the registry with Regedit and delete all signs of it.
NEVER PAY!
I totally support what Tony says "NEVER PAY!" - a friend recently did and of course your system is not restored you just lost your money to some fraudster. I'm no computer whizz-kid but thanks to all the helpful advice I got from this website I have been able to successfully restore my system whilst running in SAFEMODE and have now run security software and removed the virus. I'm so pleased - thanks again.
This has happened twice on my dads computer.
First time he took it to a PC shop who charged £120.00 to wipe windows and install new virus protection (AVG).
Within 3 days of having the laptop back the same thing happened again. AVG does not recognise it as a virus and after doing several scans it reports "no threats". Does this thing bypass all antivirus software???
Ukash is an official payments system used via newsagents in France. Their UK HQ say transactions are anonymous but they are willing to identify to whom money was sent on a police request (if taken off a police demand Ukash page)
Had a problem with Ukash virus, I have a number of accounts on one lap top, the virus only affected one account, I was able to solve the problem by loggin on to another account and setting my lap top to the last date my lap top was updated.. I didnt loose any documents and the Ukash virus was gone!! Hope this helps
I have just got the ukash virus, it will not even allow me to start up in safe mode without networking. any solutions HELP!!!!!
Try using safe mode with networking. It worked for me yesterday. I then got out of UKash clutches by doing system restore to the day before. Goodluck!
Rick. Try using safe mode with networking it worked for me yesterday. Then iused system restore to the day b4 to get rid of it
I live in Canada, and was a victim of the ukash virus. The banner at the top of the page said police in german. Last time I checked german wasn't an official language of Canada. Stupid hackers!
je veux un carte web UKASH
Hi. I downloaded Spyhunter 4 from your link and it confirmed I was infected by UKASH virus. When I tried to register Spyhunter it opened a read only document in word entitled safecart.com and when I tried to follow either of the links to pay I got the following message. "This operation has been canceled due to restrictions in effect on this computer.Please contact your systems administrator." I am using a stand alone home PC and have little or no technical knowledge. How do I proceed from here to register Spyhunter 4?
I have experienced ukash or similar several times on my laptop (W7-32bit) with paid DGATA-progr. and once on my desktop. Several user accounts. Restore to previous point (ctrl-alt-del admin-account restore-system) seemed to help. But i get "filename".pad (ism_0_llatsni.pad=4.3MB; lsass.exe=rundll32=44kB; dsgsdgdsgdsgw.pad=90MB !!! since restoring) desktop shortcuts/links of substantial volumes (mb). Why?
just tried to download spyhunters malware scanner to detect ukash virus from the above link
downloaded ok but my computer administrator (which is me)stopped it
any ideas or solutions on how to get it up and running welcome
Ukash evil buggers. I appreciate the candour of Fred Ives et al that you paid, but seriously, and assuming you're not just trolling, WHY would you pay ??? Surely you are joking ? And yes, altho' system restore didn't work first time, persisting with repeat attempts and frantic f8-ing got into safe mode (with command prompt) worked for me - at least, as far as regaining control, disappearing the ransom screen, and restore to previous date . . . I'm with Tony (September) - WHY would you pay ? Are there really so many people living in a police state of mind ? God help us all if so. P.S. and a Merry New Year 🙂
How to start in safe mode with internet? I don't get the same black menu with the same options as explained in other fora concerning removal of this ukash virus when pressing F8. And I can't run the Spyhunter without starting in safe mode I think. I have tried, but not in safe mode.
To remove the Ukash - Trojan from a XP System is no easy task and almost impossible. Even when starting with a current update Linux or knoppix antivirus Boot CD, none of these "Antivirus" Programs seems to find the Trojan. Which is very strange indeed. Seems to me done on purpose. And the criminals who collect the money also seem to be in the east somewhere outside Europe. But it does not get rid of the virus. You must check the registry and check with msconfig the startup programs. Ukash sits there with different names and hiding.
i tried with safemode i didnt work
just start the pc whitout internet connection (in this case you won't be bothered with ukash), then simply start system restore to a previous date when the pc was not infected yet!!!!
I have been attacked by the Ukash virus. Fortunately I was able to boot in F8 mode and go to a previous restore point. Some damage has been done. I can't open JPEG,PDF.WORD.Excel files. Internet Explorer is acting strange. my favourites don't open anymore. I have downloaded all sorts of anti malware/syware/virus tools via a clean computer to USB stick. These programs seem to be a scam in themself. The ones that charge seem to find hundreds of problems. scare the s...t out of you so you pay o and register to get them cleaned. The free programs find little or nothing. It's all bull
My fix: Boot in Safe Mode with Command Prompt. Type "regedt32.exe". Search for "winlogon". It will find a few different entries but you need one with a key called "shell". It will say something like "explorer.exe,c:\users\...\skype.dat" make it just explorer.exe. Reboot.
Thanks Fred Jenkinson. Worked like a charm to remove it from one of my student's computers.
hello guys! I Had same crap 3 days ago. I was able to take off screen lock by myelsf but then i found out that almost all my files are encrypted and i decide to pay $300. I was not sure that i get any codes but i had no choice. My business and system were down for 5 hours. In 1 hour after i sent moneypak code i receive codes for encrypted files and after paste codes in fields it start decrypting files and everything back to normal.Here are codes for decrypting i received, try them to decrypt files maybe its gonna be work for you guys too :First Passcode: Nope Not Here buddySecond Passcode: Nope Not Here buddy
I have a virus called PUP.bProtector and I don't have money to remove. I'v been printing every piece of info. about it and now have came up with this site. Will someone please with everything they know help me
Has anyone run into the Ukash virus leaving a file called: \Appdata\Roaming\"wkbtwb",set_error_fn in the reg file?
ty t the people above for yer info i restored my pc via safe mode with prompts and it removed the ukash screen completely..
The Virus allows me to boot up into Safe Mode but the taskbar at the bottom with Start Button only appears on screen for a split second and then closes windows down and then the Metropolitan Police Screen appears so cannot get in to the Control Panel.
I think this virus has 'evolved'. I've got it on an old Toughbook running XP Service Pack3. I have tried everything to get it to run in safe mode but it just won't have it. Even Comodo's rescue disk is ignored. And I suspect that most of the sites offering fixes just install more viruses!